
September 10, 2025Use your fingerprints to unlock your phone, not a code or face.
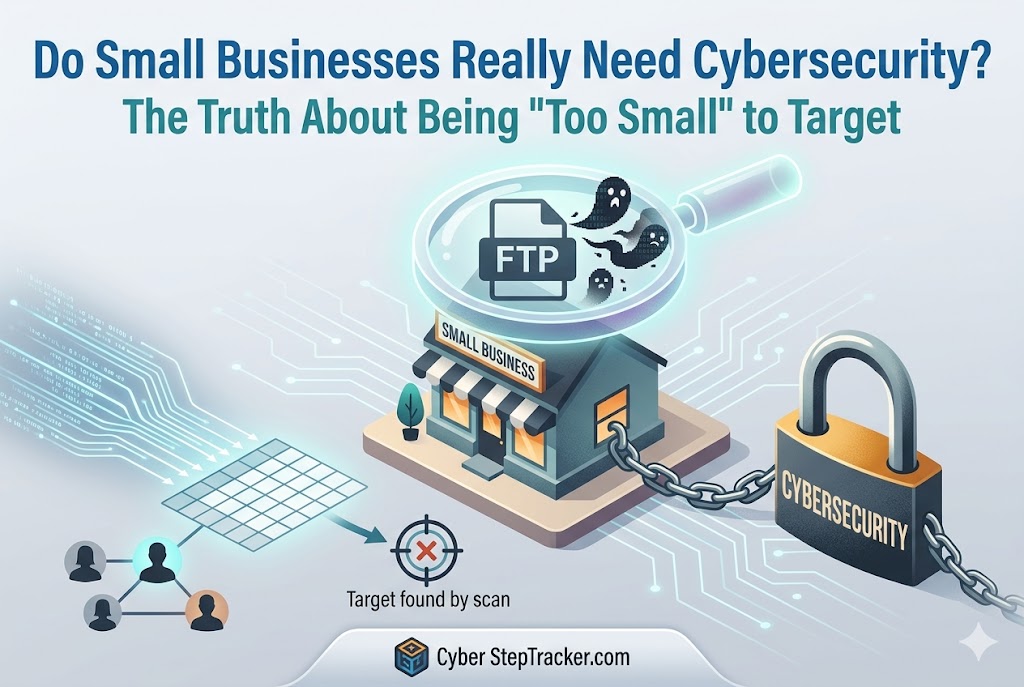
May 15, 2026We’re just a small shop. Why would a hacker care about us?
It’s a question we hear constantly from business owners: "We’re just a small shop. Why would a hacker care about us? We aren't a big bank or a massive retailer."
It sounds logical. It sounds safe. But as we learned firsthand, that logic is one of the most dangerous myths in the modern business world.
A while ago, our team was performing a routine software update at a client’s site. It was supposed to be a standard procedure—nothing out of the ordinary. But as we dug into the system, we noticed something strange.
We discovered an FTP-type virus lurking in their network. It had infected every single Windows machine running an FTP server.
There was no ransom note. No files had been deleted. No money had been stolen. However, the "cleanup" was an intensive process. We had to walk the client through disabling the virus, scrubbing the systems, and resetting passwords across their entire site.
The silver lining? Once the virus was gone, their system actually ran significantly faster! But the wake-up call was loud and clear: even if you aren't the target, you can still be the victim.
The idea that hackers only go after the big players is simply wrong.
Hackers aren't usually sitting at a desk, manually typing in names of companies they want to rob. They use automated tools. They use lists containing millions of email addresses and website URLs. They hit "Go" and let the bots do the work.
If you have a website, an email address, or both, you are on a list. To a hacker, you aren't a "small business"—you are just another entry on a spreadsheet. The goal isn't to find you specifically; the goal is to find anyone with a vulnerability.
The best defense isn't being "too small to notice"; it’s being harder to attack than the next business on the list.
When people think about cyberattacks, they think about stolen credit card numbers or ransom payments. While those are devastating, there is a much more insidious hidden cost that kills small businesses: The Cost of Recovery.
When a breach happens, your staff doesn't just sit there. They are suddenly tasked with resetting passwords, auditing files, communicating with customers, and trying to get systems back online.
During those hours—or days—your team is not selling. They are not delivering services. They are not growing your business. The true cost of a cyberattack isn't just the damage to your data; it’s the massive loss of revenue caused by the total halt of your operations.
The good news is that you don't need a million-dollar IT budget to protect yourself. You can significantly increase your "defensive wall" by doing three simple things:
Subscribe to Cyber StepTracker.com for comprehensive instructions, training, and guidelines on improving your cyber security!.
That is all.
Latest Articles

September 10, 2025Use your fingerprints to unlock your phone, not a code or face.
October 14, 2025Knowing how passwords are stored helps motivate you to make and keep good passwords.
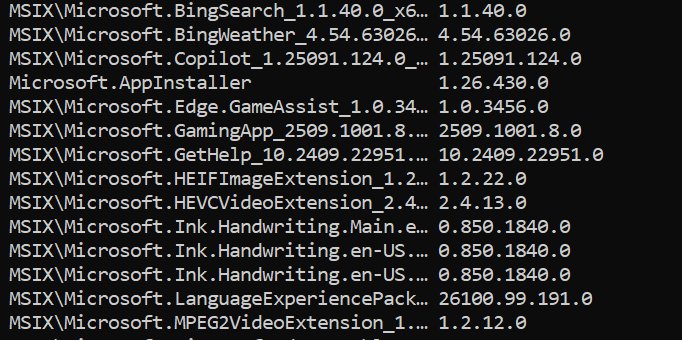
September 24, 2025 updated January 14, 2026Six different ways to list the software apps installed on your computer.
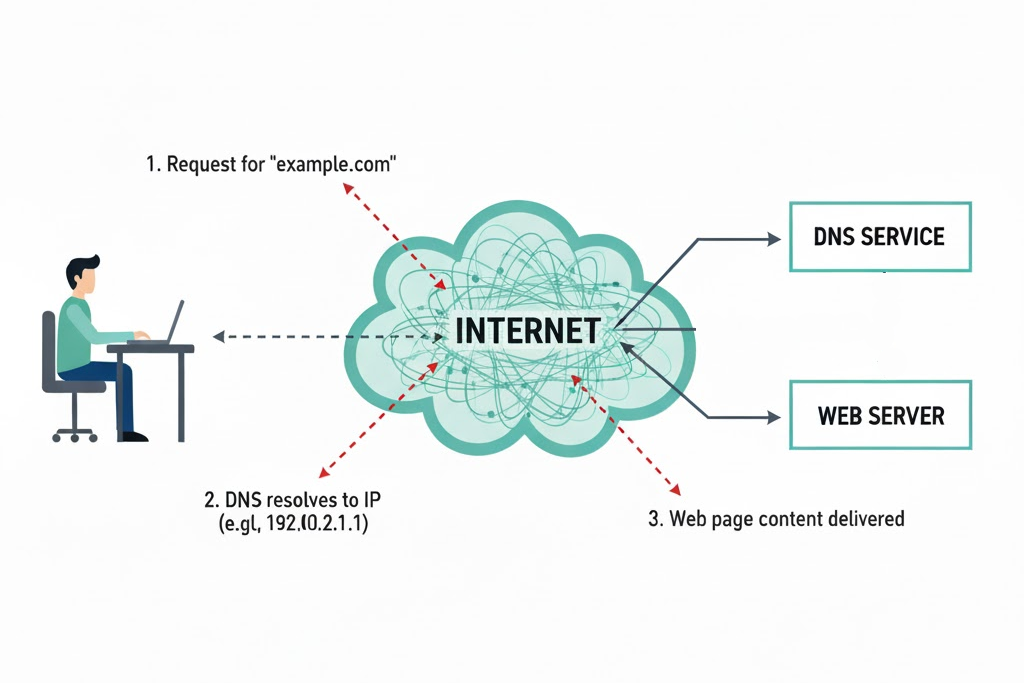
October 27, 2025 updated May 6, 2026Choose Safe DNS for Your Computer


November 19, 2025Well, could they? What are the protections on your ChatGPT sessions?
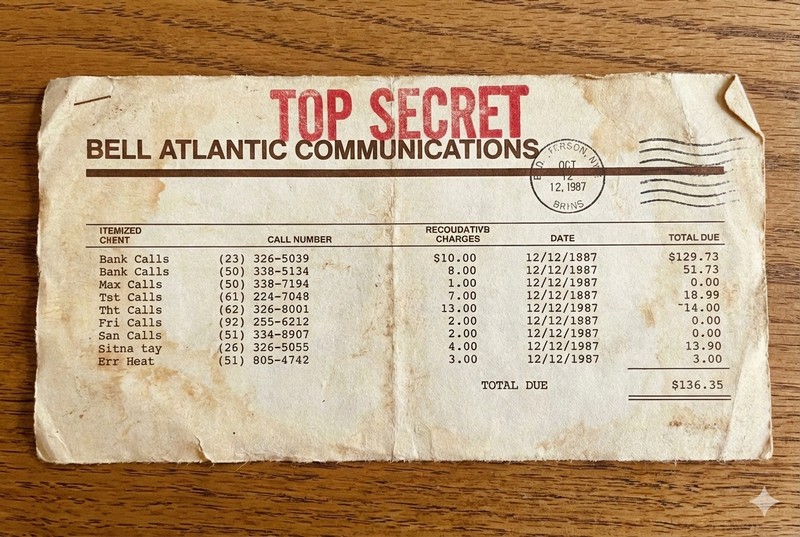
January 14, 2026Why is my telephone bill a secret? We explain the risks of people seeing your phone bill.
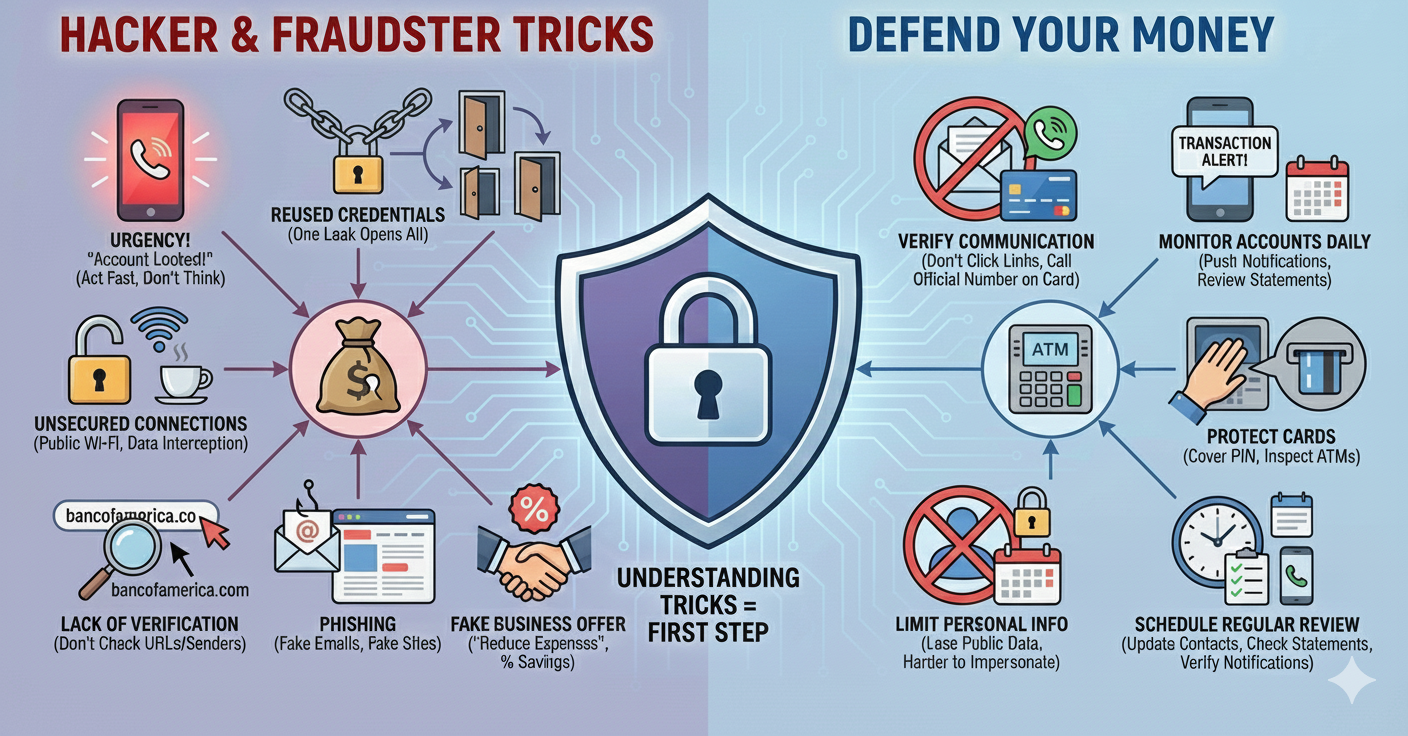
January 8, 2026How do I Defend My Money as a Small Business.

January 15, 2026 updated March 12, 2026We explain the difference between a Recovery Drive and a Windows Installation Drive, and how to use them to recover a broken PC.
February 2, 2026What are three different ways to backup my Windows computer?
May 15, 2026We’re just a small shop. Why would a hacker care about us?